
In today’s digital world, website hosting has become a common and popular choice. Cloud hosting is one type of website hosting solution. It provides excellent data storage. However, many organisations’ main concern with cloud hosting services is their security.
Many individuals do not feel comfortable with the idea of their sensitive and valuable data travelling across the internet. While cloud hosting in India, there are certain practices you can implement to secure your cloud hosting solution. Continue reading to get some tips on how to secure cloud hosting solutions.
Some Tips To Secure Cloud Hosting Solutions
Below are tips to enhance cloud hosting security. Implement these tips to enhance the security of your cloud hosting solution.
Choose A Secure Hosting Provider
When you are looking to opt for cloud hosting, it is essential to choose a reliable and secure hosting provider. Make sure you choose a provider that at least offers 99.9% guaranteed uptime. Additionally, to ensure that the hosting provider is reliable, take the help of reviews and ratings provided by other users on the cloud hosting provider.
Make sure the security infrastructure offered by the hosting provider includes protocols such as access controls, firewalls, data encryption, regular security updates, and intrusion detection systems. These measures will help secure your data and infrastructure.
Deploy A Strict Identity And Access Management (IAM)System
This system has control over who has access to the cloud’s resources. Deploying a strict identity and access management system reduces the risk of any unauthorised access to valuable data. You can implement several factors to ensure a strong and strict IAM system.
- Make sure you always use complex and strong passwords that can not be easily cracked. Additionally, regularly change these passwords to ensure the highest level of security.
- Implement MFA (multiple-factor authentication); this will ensure that all users will be required to provide additional verification, which will act as an extra layer of security.
- Implement a role-based access system based on job responsibilities; this will ensure that users only have access to the data they require.
Data Encryption
Encrypting your data converts it into an unreadable coded format. This protects your critical data from being accessed by unauthorised users.
It also protects you against financial loss that you may be caused due to data breaches. For example, if someone tries to steal your sensitive data, it will be useless to them if your data is encrypted and unreadable.
Train Your IT Security Team
Most of the data breaches are a result of human error and the recklessness of an employee. This is why training your IT security team should be the priority. This will reduce the risk of potential negligence and enhance the security of your cloud infrastructure.
Below are some points you should cover in the training of your IT security team.
- Discuss the risks associated with using personal devices at work.
- Train your IT security employees on how to appropriately handle security issues.
- Discuss with them some common cyber attack techniques like phishing. This will help them understand how to recognize and deal with such issues.
To Wrap It Up
Some common threats to cloud server security are cloud misconfiguration, unnecessary or unwarranted access, cloud vendor failure, employee error, and more.
Therefore make sure you implement the tips mentioned above to fully secure your server infrastructure and protect your valuable data.




More Stories
The Role of Technology in Scenic Fabrication
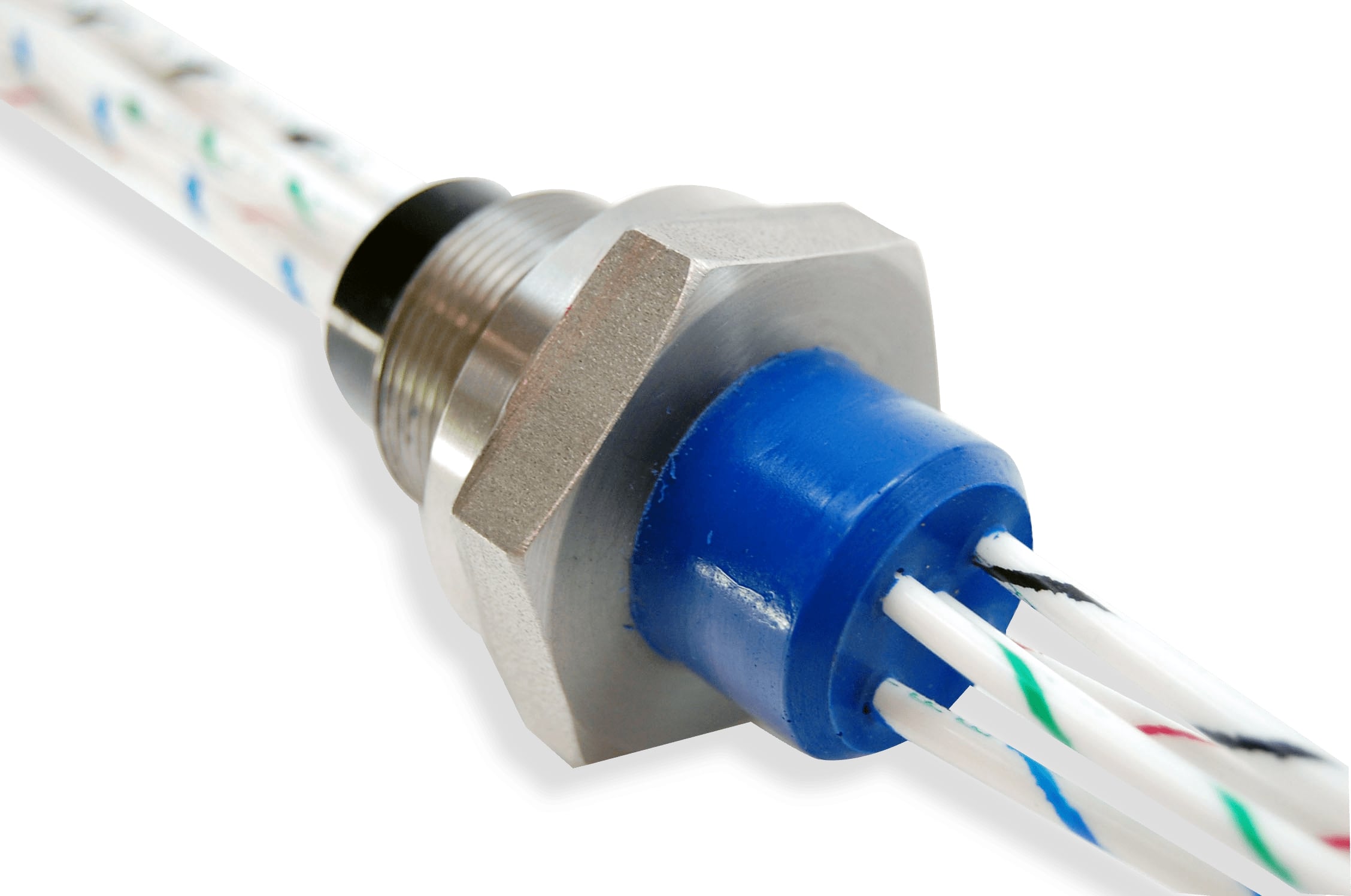
Design Considerations for Hermetic Feedthrough in Industrial Systems
Things you must know before becoming an insurance agent