Cybersecurity should be a top concern for any organization. Hackers, cybercriminals, and even rogue insiders are constantly finding sneaky new ways to steal sensitive data and disrupt critical operations. From swiping customer credit cards to hijacking corporate systems for ransomware, the threats are real.
Update, Update, Update
One of the simplest yet most impactful cybersecurity steps is keeping all your software updated to the latest secure versions. You might find those update notifications from Microsoft, Adobe, and app developers annoying, but don’t ignore or postpone them. Software updates frequently include critical security patches that fix newly discovered vulnerabilities cybercriminals could potentially exploit. Set a recurring calendar reminder to promptly install all available updates for operating systems, productivity apps, web browsers, and any other software your employees use.
Train Your Employees
Even with advanced cybersecurity software and tools deployed, your biggest vulnerability is human error and oversight. Phishing scams that trick people into revealing login credentials, or employees using ridiculously weak passwords like “password123”, are mistakes that enable the vast majority of data breaches. Provide regular, mandatory cybersecurity awareness training to educate your staff on best practices like spotting phishing emails, using strong unique passwords for every account, and staying vigilant about physical security.
Implement Multi-Factor Authentication
Using just a password to secure important accounts and systems is simply not enough in this age of widespread cyberattacks and data breaches. Multi-factor authentication adds much-needed extra layers of security, requiring a second verification step beyond just a password like a fingerprint scan or code from your smartphone. This prevents cybercriminals from accessing accounts and systems, even if they manage to steal passwords through phishing or brute-force attacks.
Embrace Risk Based Authentication
The experts at Outseer say that some of the smartest access control systems now go a step further with risk based authentication. In addition to requiring multiple verification factors, the system dynamically analyzes user behavior patterns and device fingerprints to calculate the risk level of any given login attempt. Logins from a new device in another country might be considered very high-risk and trigger additional verification hurdles. But a normal login from an employee’s recognized device would be approved as a low-risk event without added hassles. This intelligent balance enhances security posture while still preserving a smooth, convenient user experience.
Backup Your Data
Having your critical business data and systems encrypted by ransomware and held hostage is truly a nightmare scenario. Nonetheless, with consistent, redundant data backups in place using modern backup solutions, you can avoid paying ransoms to cybercriminals and simply restore your systems from backup. Implement scheduling to backup all databases, file servers, cloud storage and other repositories holding essential data to offline storage like the cloud, physical drives, or tape on a daily basis. But backups are useless if they don’t work, so be sure to regularly test the restoration process as well.
Restrict Privileges
Following the fundamental principle of least privilege philosophy helps prevent unnecessary security risks and contain potential damage. Only provide users with the absolute minimum level of data and system access privileges required for their specific roles and duties. This limits the potential blast radius and severity in the event of compromised user accounts.
Conclusion
The cybersecurity landscape is continuously shifting and evolving as innovative new tactics and threats emerge. Staying on top of these smart defense best practices while monitoring emerging trends is crucial for protecting your business from potentially devastating attacks and breaches. Consult trusted cybersecurity experts, make security awareness an ingrained part of your culture, and ensure shoring up defenses remains an ongoing priority. With diligence, your critical data, assets, and operations can be safeguarded.




More Stories
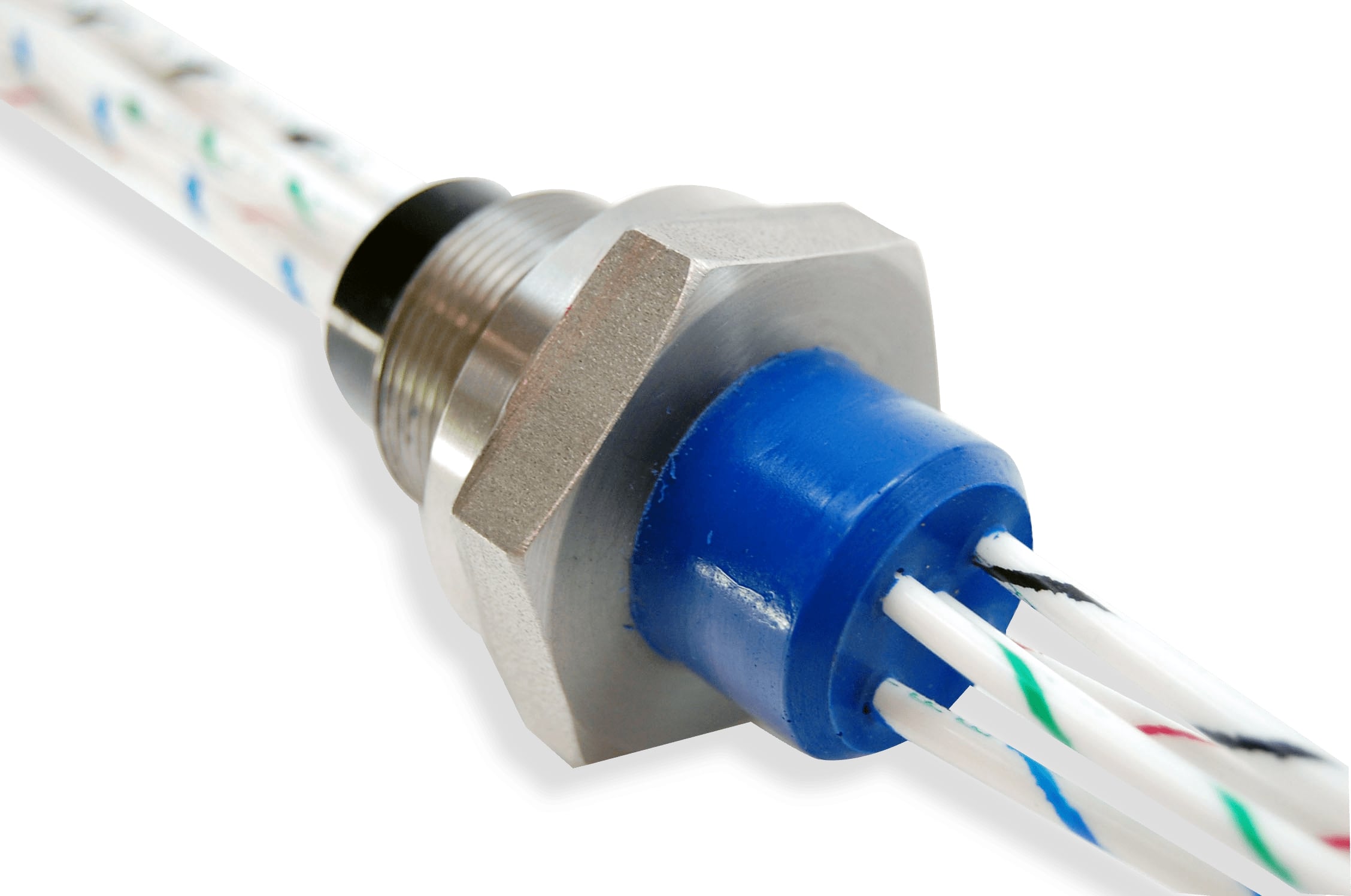
Design Considerations for Hermetic Feedthrough in Industrial Systems
Things you must know before becoming an insurance agent
Expert Professional Services Tailored to Your Unique Needs